The OSI model is an essential tool for understanding how a network operates. It’s also an essential tool when it comes to cybersecurity. Understanding the 7 stages of the OSI model and the cyber threats that exist at each layer will greatly improve your network security. A layer-by-layer approach to cybersecurity following the OSI model is one of the most thorough and effective methods for conducting penetration testing, allowing you to identify and remediate any vulnerabilities in your network and prevent cyber attacks.
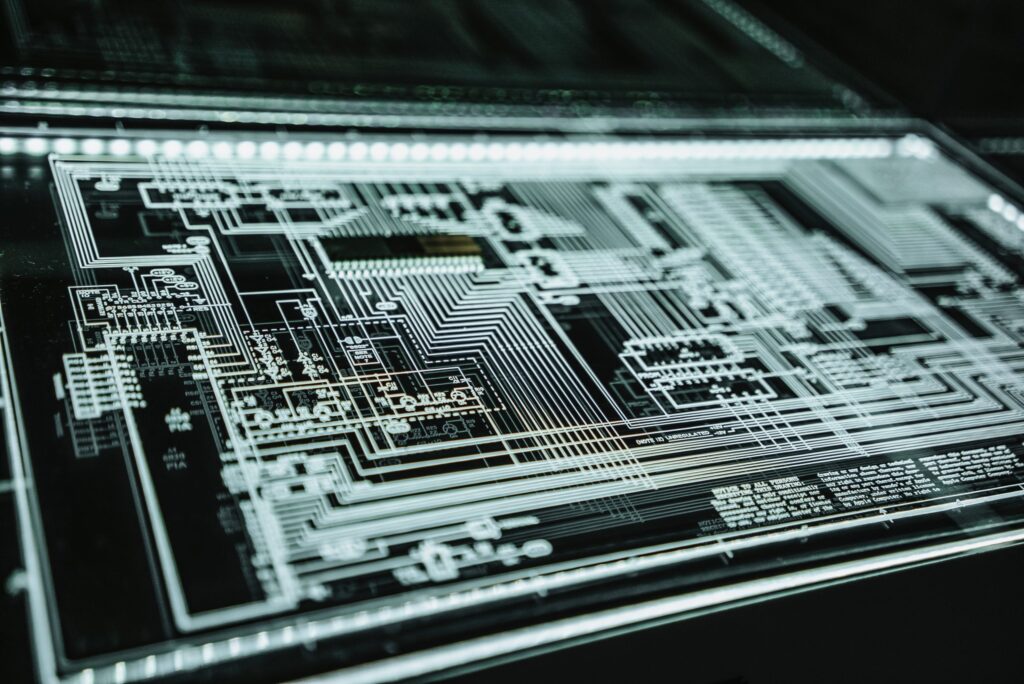
What is the OSI model?
The Open Systems Interconnection model, or OSI model, describes the way a network system communicates, or how data is exchanged between point A and point B. It breaks down the flow of a network into 7 different stages. Below, you’ll find basic descriptions of each stage.
1. Physical
At the base of the OSI model is the physical layer. This layer represents the electrical and physical components of your system. These components include cables, routers, modems, and other physical requirements.
2. Data Link
This layer manages data and information that are exchanged across the same physical network.
3. Network
The network layer is where most router functions occur. This is the exchange of data and information between different servers.
4. Transport
This layer coordinates the transfer of data between systems and hosts. It defines how much data is being sent, the rate it’s being sent, where the data is going and more.
5. Session
When two devices, computers or servers communicate with each other, a session is generated. The session layer sets up the session, coordinates the responses and terminates the session when it ends.
6. Presentation
The presentation layer is where data is translated from its network form into its application form. In other words, it presents data to the application. This is also where encryption and decryption happen. (Take a look at our blog on SSL Certificates, which are a large part of the presentation layer.)
7. Application
This is the layer that the user directly interacts with. Applications include web browsers, Microsoft Office, Skype, and many more.
Why is the OSI model important to cybersecurity?
Wherever there is a function being performed, there is a possibility for disfunction. There are several possible cyberattacks at each of the seven layers of your network. Listed below are just a few of those potential attacks:
Physical – When you think of “cyber attack” you might not associate it with something tangible, but threats do exist at the physical layer. Attacks at the physical layer are usually DoS, or Denial of Service, attacks. The goal of these attacks is to stop all network functions. Examples of DoS attacks at the physical layer include a wire being cut, or a wireless connection being interrupted.
Data Link – Attacks at the Data Link layer come from within the local network, or LAN. It’s important to educate all your network users on how to prevent cyber attacks. Otherwise, they may unknowingly put your network at risk. Data Link attacks may include MAC Flooding or ARP poisoning, which are usually a result of unhardened routers.
Network – Network layer attacks, unlike attacks at the Data Link layer, can be performed over the internet. There are more DoS attacks possible at this layer such as ping floods or ICMP attacks.
Transport – The main threat at the Transport layer is port scanning. This attack seeks out open or unused network ports and exploits these weaknesses in order to access your data.
Session, Presentation and Application – The attacks that occur at these layers are primarily related to flaws in code. As a result, attackers can implement their own code into your network and extract data. An example of this is SQL injection. Again, educating your team on best practices is crucial to preventing these attacks.
How do you implement the OSI model into your own security plan?
The OSI model is a valuable tool that will help you identify cyber threats wherever they exist and effectively secure your network. However, cyber protection does not end there—it is an ongoing process. Beyond the OSI model, there are additional tools that should be implemented into our cybersecurity plan in order to achieve complete protection. This can be a complicated and time-consuming process if you try to go it alone. Employing experts to help will save you time and give your network more intensive protection.
The cybersecurity team at Fortress has the industry knowledge that you may lack to help secure your network. Not only does Fortress approach cybersecurity using the OSI model, but they also employ other industry-leading tools to further strengthen your network. In addition, we provide support online and on-site, and educate you and your team on how to better protect yourselves in-house.
Don’t wait for an attack to happen before securing your network. Visit our cyber page at https://gofortress.com/cyber to learn more about the powerful suite of Fortress cybersecurity services and to request a free security audit.